Industries
IT audit firms & freelancers
External IT auditors face the daunting task of ensuring compliance with standards such as ISA (315), ISO 27002, NIS2, NIST and CIS. Easy2audit supports them by offering detailed data analysis across diverse IT environments, simplifying the auditing process and minimising disruptions for their clients.
Generate summarised IT audit reports
Generate summarised IT audit reports
Generate summarised IT audit reports



NIS2
ISO 27002
NIST
ISA 315
CIS v8
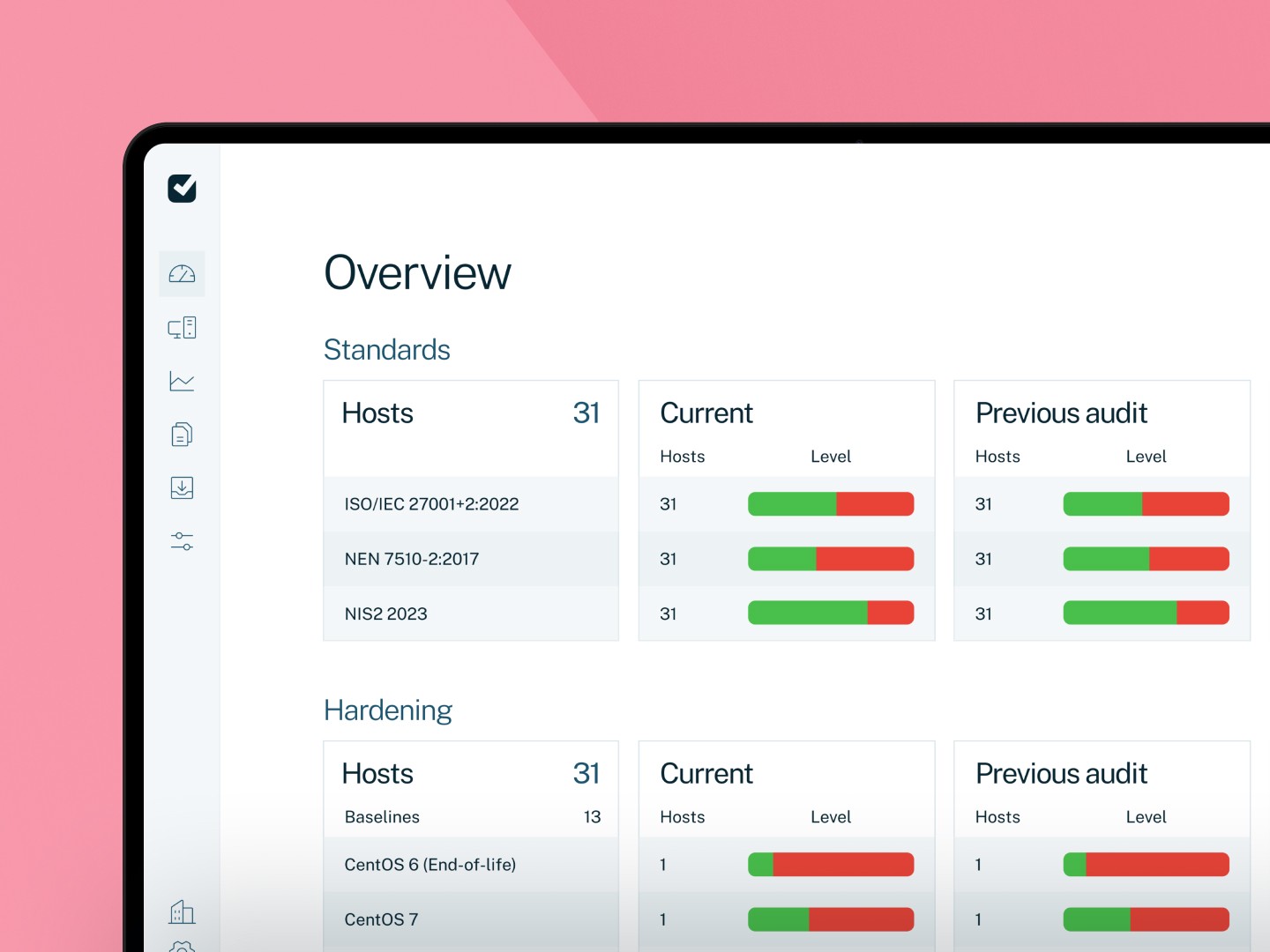
Maximise audit efficiency with automated audit reporting
Automate audit process, save time and meet regulatory standards.
Data analysis
Streamline your audit processes with automated data collection and analysis, reducing time spent on manual tasks.
Compliance made easy
Easily meet regulatory standards with predefined report templates, ensuring thorough and compliant audits.
Efficient auditing
Enhance audit efficiency, saving time and reducing errors, allowing for a more focused and effective audit experience.
Password length is 8 instead of 14

Maximise audit efficiency with automated audit reporting
Automate audit process, save time and meet regulatory standards.
Data analysis
Streamline your audit processes with automated data collection and analysis, reducing time spent on manual tasks.
Compliance made easy
Easily meet regulatory standards with predefined report templates, ensuring thorough and compliant audits.
Efficient auditing
Enhance audit efficiency, saving time and reducing errors, allowing for a more focused and effective audit experience.
Password length is 8 instead of 14

Maximise audit efficiency with automated audit reporting
Automate audit process, save time and meet regulatory standards.
Data analysis
Streamline your audit processes with automated data collection and analysis, reducing time spent on manual tasks.
Compliance made easy
Easily meet regulatory standards with predefined report templates, ensuring thorough and compliant audits.
Efficient auditing
Enhance audit efficiency, saving time and reducing errors, allowing for a more focused and effective audit experience.
Password length is 8 instead of 14

Gain direct insights into your client’s Active Directory
Monitor critical IT controls effortlessly, by gaining valuable insights.
9 enterprise adminstrators are active
26% of the users inactive
2935 total users

Antivirus
Antivirus software: Ensure it's active and up-to-date across all systems.
Updates & Vulnerabilities
Updates (Patching) & Vulnerabilities (CVEs): Stay informed about OS updates and potential vulnerabilities.
Logical access
Logical access control & Authorizations: Access detailed insights into Active Directory, SQL User details, and Fine-Grained Policies.
Hardening
Security Configurations (Hardening): Assess and enhance security configurations for optimal protection.
Gain direct insights into your client’s Active Directory
Monitor critical IT controls effortlessly, by gaining valuable insights.
9 enterprise adminstrators are active
26% of the users inactive
2935 total users

Antivirus
Antivirus software: Ensure it's active and up-to-date across all systems.
Updates & Vulnerabilities
Updates (Patching) & Vulnerabilities (CVEs): Stay informed about OS updates and potential vulnerabilities.
Logical access
Logical access control & Authorizations: Access detailed insights into Active Directory, SQL User details, and Fine-Grained Policies.
Hardening
Security Configurations (Hardening): Assess and enhance security configurations for optimal protection.
Gain direct insights into your client’s Active Directory
Monitor critical IT controls effortlessly, by gaining valuable insights.
9 enterprise adminstrators are active

Antivirus
Antivirus software: Ensure it's active and up-to-date across all systems.
Updates & Vulnerabilities
Updates (Patching) & Vulnerabilities (CVEs): Stay informed about OS updates and potential vulnerabilities.
Logical access
Logical access control & Authorizations: Access detailed insights into Active Directory, SQL User details, and Fine-Grained Policies.
Hardening
Security Configurations (Hardening): Assess and enhance security configurations for optimal protection.
Independence without Debate
What matters most to auditors
Easy2audit is designed to fully respect the independent role of the external auditor. The tool strictly measures and reports and does not perform any configuration changes or operational actions within client environments.
Reliable and reproducible audit evidence
Measurements are consistent, repeatable, and verifiable. Findings remain traceable over time and across environments, which is essential for reviews and assurance engagements.
Transparency in methodology and technology
Easy2audit does not operate as a black box. The scripts used and the resulting output files are transparent and can be clearly explained to clients, reviewers, and regulators.
Efficiency without loss of quality
Easy2audit does not operate as a black box. The scripts used and the resulting output files are transparent and can be clearly explained to clients, reviewers, and regulators.
Alignment with widely used standards
Easy2audit supports audits based on, among others, NIS2, ISO 27001/27002, BIO, NEN 7510, DORA, and CIS Benchmarks, with a focus on the actual technical configuration of systems.
Independence without Debate
What matters most to auditors
Easy2audit is designed to fully respect the independent role of the external auditor. The tool strictly measures and reports and does not perform any configuration changes or operational actions within client environments.
Reliable and reproducible audit evidence
Measurements are consistent, repeatable, and verifiable. Findings remain traceable over time and across environments, which is essential for reviews and assurance engagements.
Transparency in methodology and technology
Easy2audit does not operate as a black box. The scripts used and the resulting output files are transparent and can be clearly explained to clients, reviewers, and regulators.
Efficiency without loss of quality
Easy2audit does not operate as a black box. The scripts used and the resulting output files are transparent and can be clearly explained to clients, reviewers, and regulators.
Alignment with widely used standards
Easy2audit supports audits based on, among others, NIS2, ISO 27001/27002, BIO, NEN 7510, DORA, and CIS Benchmarks, with a focus on the actual technical configuration of systems.
Independence without Debate
What matters most to auditors
Easy2audit is designed to fully respect the independent role of the external auditor. The tool strictly measures and reports and does not perform any configuration changes or operational actions within client environments.
Reliable and reproducible audit evidence
Measurements are consistent, repeatable, and verifiable. Findings remain traceable over time and across environments, which is essential for reviews and assurance engagements.
Transparency in methodology and technology
Easy2audit does not operate as a black box. The scripts used and the resulting output files are transparent and can be clearly explained to clients, reviewers, and regulators.
Efficiency without loss of quality
Easy2audit does not operate as a black box. The scripts used and the resulting output files are transparent and can be clearly explained to clients, reviewers, and regulators.
Alignment with widely used standards
Easy2audit supports audits based on, among others, NIS2, ISO 27001/27002, BIO, NEN 7510, DORA, and CIS Benchmarks, with a focus on the actual technical configuration of systems.
Create reports easily
Comprehensive reporting for external audits
Offering a range of reports for external IT auditors, covering compliance, risk assessments, cybersecurity analysis, and audit trails, all tailored for in-depth insights and thorough audit support.
IT-audit summary
Outline critical security measures of an operating system, centred on key ITGCs. Cover local account policies, including password policies and lockout protocols, along with additional hardening settings.
View sample report
Active Directory & EntraID
Crafted with input from IT auditors across various firms, both small and large, these reports display the rights, privileges, and various other security-related attributes of AD users.
View sample report
SQL
Databases harbor extensive and vital data, necessitating an analysis of user activity, privileges, and behaviour to safeguard against misuse of accounts.
View sample report
System configurations (hardening)
Default operating system configurations prioritise usability over security, leaving vulnerabilities for cybercriminals. Adjusting these configurations is a critical cybersecurity measure.
View sample report
Create reports easily
Comprehensive reporting for external audits
Offering a range of reports for external IT auditors, covering compliance, risk assessments, cybersecurity analysis, and audit trails, all tailored for in-depth insights and thorough audit support.
IT-audit summary
Outline critical security measures of an operating system, centred on key ITGCs. Cover local account policies, including password policies and lockout protocols, along with additional hardening settings.
View sample report
Active Directory & EntraID
Crafted with input from IT auditors across various firms, both small and large, these reports display the rights, privileges, and various other security-related attributes of AD users.
View sample report
SQL
Databases harbor extensive and vital data, necessitating an analysis of user activity, privileges, and behaviour to safeguard against misuse of accounts.
View sample report
System configurations (hardening)
Default operating system configurations prioritise usability over security, leaving vulnerabilities for cybercriminals. Adjusting these configurations is a critical cybersecurity measure.
View sample report
Create reports easily
Comprehensive reporting for external audits
Offering a range of reports for external IT auditors, covering compliance, risk assessments, cybersecurity analysis, and audit trails, all tailored for in-depth insights and thorough audit support.
IT-audits summary reports
Outline critical security measures of an operating system, centred on key ITGCs. Cover local account policies, including password policies and lockout protocols, along with additional hardening settings.
View sample report
Active Directory reports
Crafted with input from IT auditors across various firms, both small and large, these reports display the rights, privileges, and various other security-related attributes of AD users.
View sample report
SQL reports
Databases harbor extensive and vital data, necessitating an analysis of user activity, privileges, and behaviour to safeguard against misuse of accounts.
View sample report
System configuration reports
Default operating system configurations prioritise usability over security, leaving vulnerabilities for cybercriminals. Adjusting these configurations is a critical cybersecurity measure.
View sample report
IT-audits summary reports
Outline critical security measures of an operating system, centred on key ITGCs. Cover local account policies, including password policies and lockout protocols, along with additional hardening settings.
View sample report
Active Directory reports
Crafted with input from IT auditors across various firms, both small and large, these reports display the rights, privileges, and various other security-related attributes of AD users.
View sample report
SQL reports
Databases harbor extensive and vital data, necessitating an analysis of user activity, privileges, and behaviour to safeguard against misuse of accounts.
View sample report
System configuration reports
Default operating system configurations prioritise usability over security, leaving vulnerabilities for cybercriminals. Adjusting these configurations is a critical cybersecurity measure.
View sample report
IT-audits summary reports
Outline critical security measures of an operating system, centred on key ITGCs. Cover local account policies, including password policies and lockout protocols, along with additional hardening settings.
View sample report
Active Directory reports
Crafted with input from IT auditors across various firms, both small and large, these reports display the rights, privileges, and various other security-related attributes of AD users.
View sample report
SQL reports
Databases harbor extensive and vital data, necessitating an analysis of user activity, privileges, and behaviour to safeguard against misuse of accounts.
View sample report
System configuration reports
Default operating system configurations prioritise usability over security, leaving vulnerabilities for cybercriminals. Adjusting these configurations is a critical cybersecurity measure.
View sample report
IT-audits summary reports
Outline critical security measures of an operating system, centred on key ITGCs. Cover local account policies, including password policies and lockout protocols, along with additional hardening settings.
View sample report
Active Directory reports
Crafted with input from IT auditors across various firms, both small and large, these reports display the rights, privileges, and various other security-related attributes of AD users.
View sample report
SQL reports
Databases harbor extensive and vital data, necessitating an analysis of user activity, privileges, and behaviour to safeguard against misuse of accounts.
View sample report
System configuration reports
Default operating system configurations prioritise usability over security, leaving vulnerabilities for cybercriminals. Adjusting these configurations is a critical cybersecurity measure.
View sample report
Solutions
Customised solutions for efficient auditing and precise remediation
We offer customised solutions to support your auditing process, providing detailed insights tailored to your specific needs.
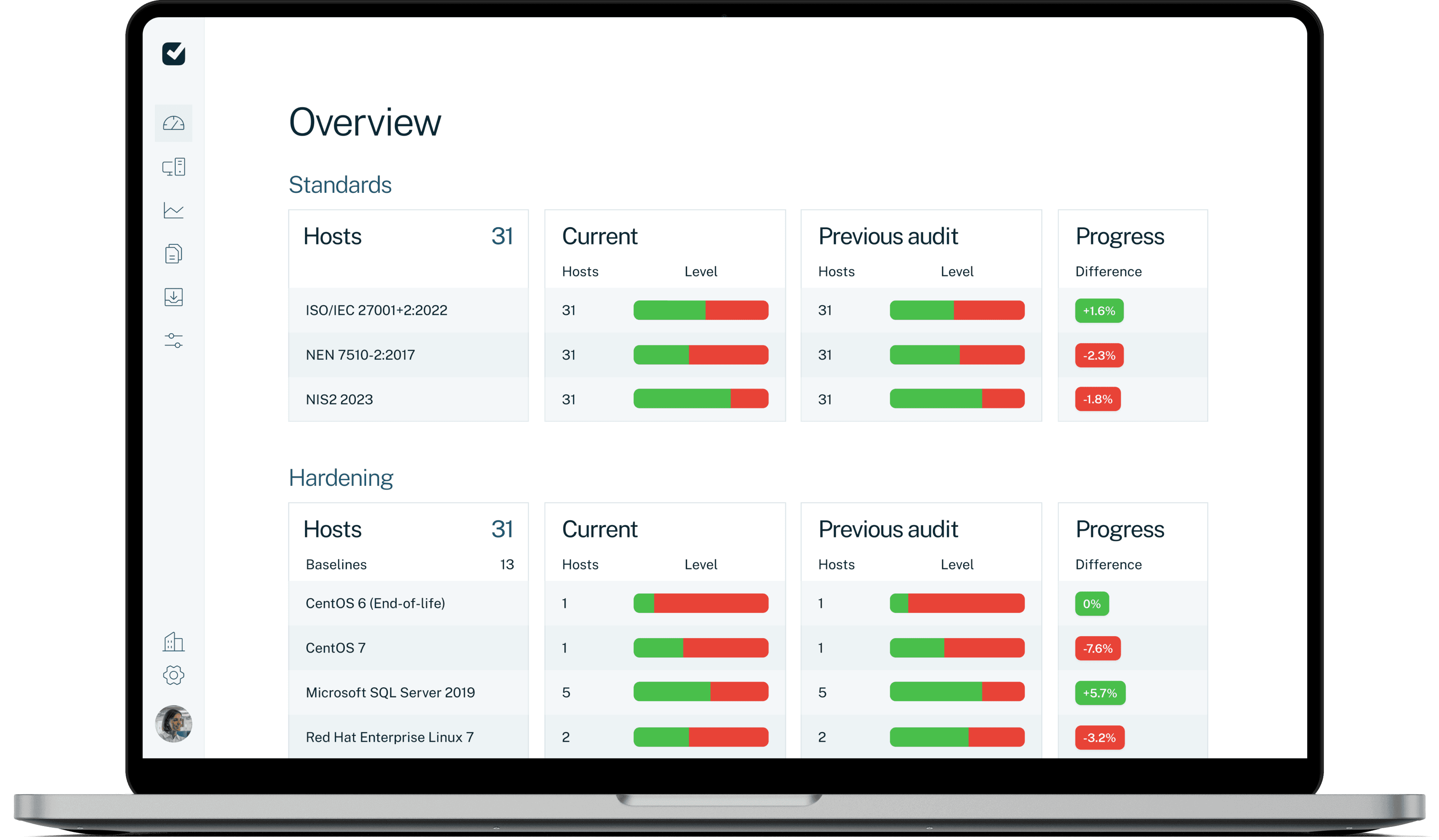
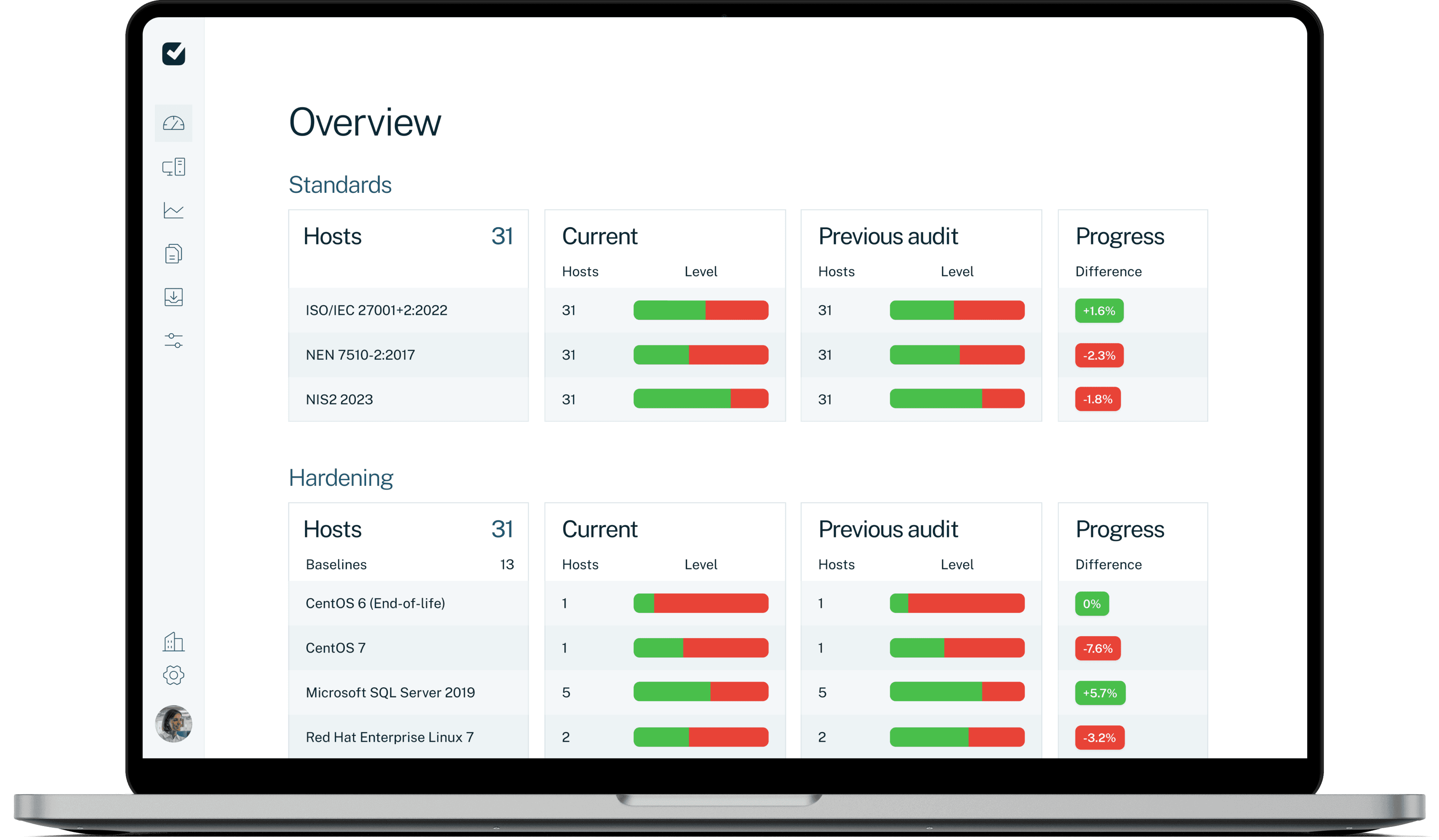
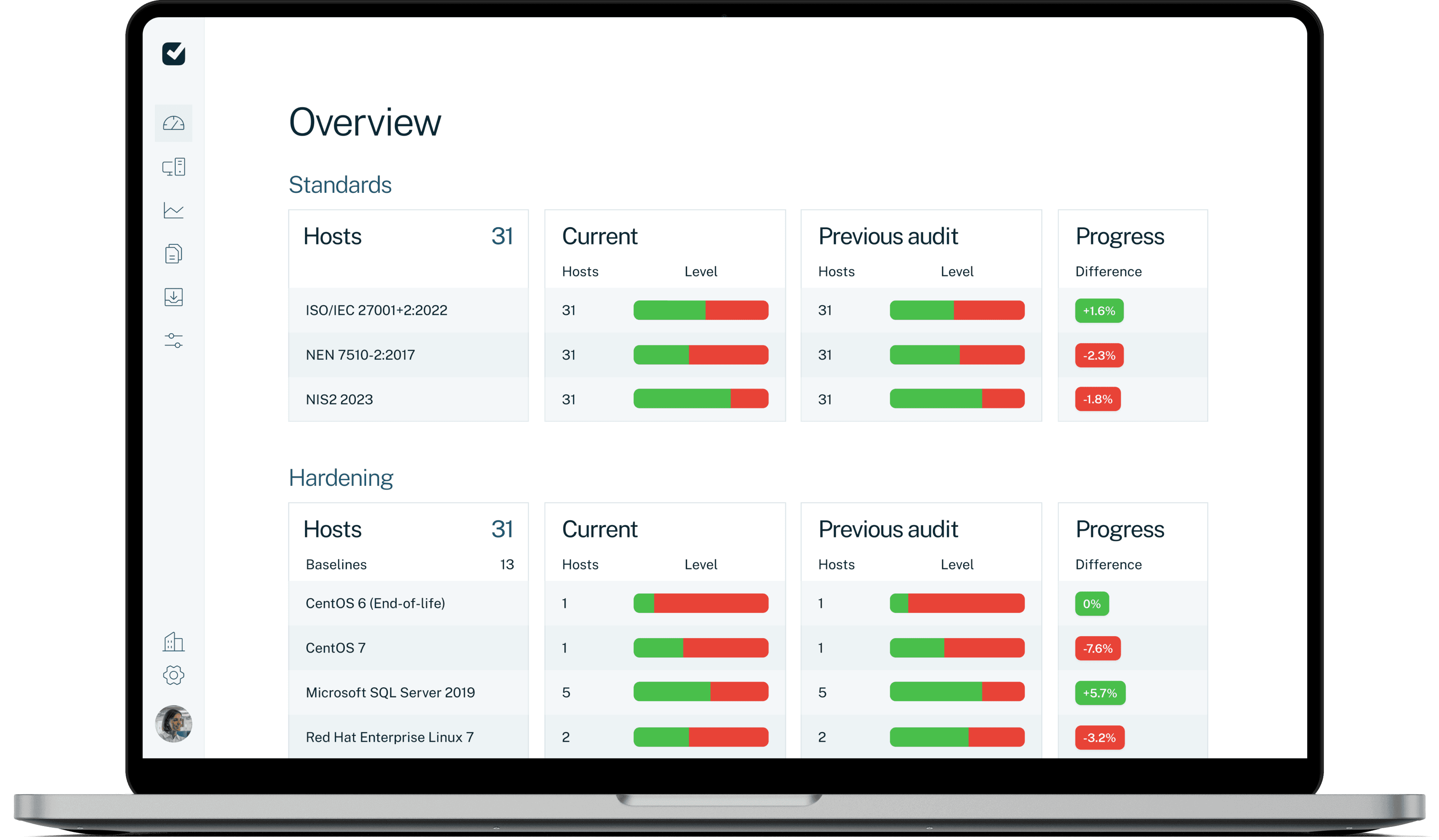
Maximize your cyber security with system hardening
Benchmark your systems against standards like NIST, CIS, and ISO for detailed controls, explanations, and mitigation recommendations. All in one single overview.

Identify which user accounts need to be removed or have unused functions disabled.
View the secure values assigned to security settings.
Identify default passwords and update them to improve security.
Solutions
Customised solutions for efficient auditing and precise remediation
We offer customised solutions to support your auditing process, providing detailed insights tailored to your specific needs.
Maximize your cyber security with system hardening
Benchmark your systems against standards like NIST, CIS, and ISO for detailed controls, explanations, and mitigation recommendations. All in one single overview.

Identify which user accounts need to be removed or have unused functions disabled.
View the secure values assigned to security settings.
Identify default passwords and update them to improve security.
Solutions
Customised solutions for efficient auditing and precise remediation
We offer customised solutions to support your auditing process, providing detailed insights tailored to your specific needs.
Maximize your cyber security with system hardening
Benchmark your systems against standards like NIST, CIS, and ISO for detailed controls, explanations, and mitigation recommendations. All in one single overview.

Identify which user accounts need to be removed or have unused functions disabled.
View the secure values assigned to security settings.
Identify default passwords and update them to improve security.
Impact of using Easy2audit
Time-saving
Our solution saves you and your clients valuable time, allowing you to complete audits in a fraction of the time it would take to do them manually.
Automated
Our automated solution scans and produces reports with just a few clicks. With the time saved you can provide more value to your clients.
One system
Access all your clients’ systems in one dashboard, filtering based on your requirements. You can even assign employees to only have access to their own clients.
Partnerships we are proud of


Impact of using Easy2audit
Time-saving
Our solution saves you and your clients valuable time, allowing you to complete audits in a fraction of the time it would take to do them manually.
Automated
Our automated solution scans and produces reports with just a few clicks. With the time saved you can provide more value to your clients.
One system
Access all your clients’ systems in one dashboard, filtering based on your requirements. You can even assign employees to only have access to their own clients.
Partnerships we are proud of


Impact of using Easy2audit
Time-saving
Our solution saves you and your clients valuable time, allowing you to complete audits in a fraction of the time it would take to do them manually.
Automated
Our automated solution scans and produces reports with just a few clicks. With the time saved you can provide more value to your clients.
One system
Access all your clients’ systems in one dashboard, filtering based on your requirements. You can even assign employees to only have access to their own clients.
Partnerships we are proud of


What our customers say
What our customers say
Resources
The latest insights
Discover the latest industry news, interviews, and other insightful content.
Resources
The latest insights
Discover the latest industry news, interviews, and other insightful content.
Resources
The latest insights
Discover the latest industry news, interviews, and other insightful content.
Frequently asked questions
Everything you need to know about the product and billing.
Easy2audit script
Easy2audit uses scripts. What kind of scripts are they?
The Easy2audit scripts are developed in-house and are specifically designed to read configuration settings.
Is there one script or multiple scripts?
Will the Easy2audit scripts impact the stability of my server?
How does the script read the settings?
What permissions do the scripts need to be run?
Do the scripts change the configuration settings?
Do the scripts create temporary files?
Where do the scripts save the results?
Can I view the scripts before I run them?
IT General Controls (ITGC)
What are IT General Controls (ITGC)?
Which IT General Controls (ITGC) does Easy2Audit address?
Frequently asked questions
Everything you need to know about the product and billing.
Easy2audit script
Easy2audit uses scripts. What kind of scripts are they?
The Easy2audit scripts are developed in-house and are specifically designed to read configuration settings.
Is there one script or multiple scripts?
Will the Easy2audit scripts impact the stability of my server?
How does the script read the settings?
What permissions do the scripts need to be run?
Do the scripts change the configuration settings?
Do the scripts create temporary files?
Where do the scripts save the results?
Can I view the scripts before I run them?
IT General Controls (ITGC)
What are IT General Controls (ITGC)?
Which IT General Controls (ITGC) does Easy2Audit address?
Frequently asked questions
Everything you need to know about the product and billing.
Easy2audit script
Easy2audit uses scripts. What kind of scripts are they?
The Easy2audit scripts are developed in-house and are specifically designed to read configuration settings.
Is there one script or multiple scripts?
Will the Easy2audit scripts impact the stability of my server?
How does the script read the settings?
What permissions do the scripts need to be run?
Do the scripts change the configuration settings?
Do the scripts create temporary files?
Where do the scripts save the results?
Can I view the scripts before I run them?
IT General Controls (ITGC)
What are IT General Controls (ITGC)?
Which IT General Controls (ITGC) does Easy2Audit address?
Ready to upgrade your IT audits?
Identify and mitigate risks

Etienne Schraven
Director

Ready to upgrade your IT audits?
Identify and mitigate risks

Etienne Schraven
Director